Most security teams believe they know what they are protecting until an incident proves otherwise.
Traditional asset inventories are static, incomplete, and quickly outdated. Remote work, unmanaged devices, and decentralised IT have created blind spots that attackers actively exploit. Security and IT teams are left stitching together data from multiple tools, spreadsheets, and scans, without a reliable source of truth.
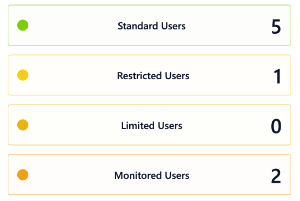
4Remote delivers continuous asset discovery and intelligence across remote, unmanaged, and corporate environments, creating a single source of truth for security and IT teams.
Assets are automatically identified and monitored in real time, without relying on manual input or outdated inventories.
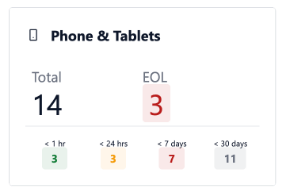
Assets are automatically identified and monitored in real time, without relying on manual input or outdated inventories.
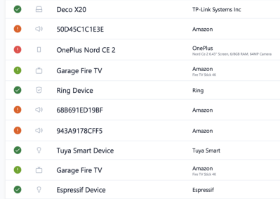
Assets are automatically identified and monitored in real time, without relying on manual input or outdated inventories.
Accurate asset intelligence becomes the foundation for policy-driven access, remediation, and enforcement..