Most organisations still rely on trust models that assume users and devices are safe once connected.
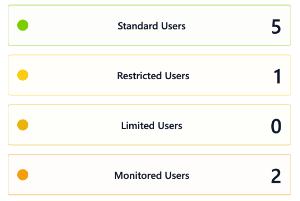
VPNs extend the network perimeter to insecure environments. Users often retain excessive privileges long after they need them. Device health, network context, and real-time risk are rarely considered once access is granted.
4Remote delivers practical, deployable zero trust, grounded in real asset visibility and continuous risk assessment.
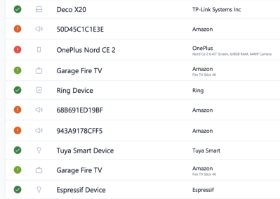
Every access request is evaluated in real time using identity, device posture, network context, and risk signals.
Access decisions adapt dynamically based on changing conditions, not static rules or network location.
Users and devices only receive the minimum access required, limiting lateral movement during incidents.
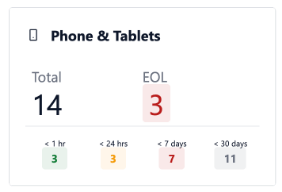
Accurate asset intelligence ensures policies are based on reality, not assumptions.
Move away from perimeter-based access models without disrupting users.
Ensure only trusted users and devices can access critical services.
Limit the impact of compromised credentials or malicious insiders.
Support zero trust principles aligned with modern frameworks and regulations.